Keeping data on cloud servers is simple due to automatic backups or drag-and-drop interfaces while also providing an easy solution to the giant demand for digital storage. Doing so has the advantage of providing access to your files when your device crashes while also keeping them tidy. However, security is a major concern causing people to ask, “How safe is cloud storage?” and the short answer is, it’s very safe.
Connected Platforms presents this overview of cloud storage security to help you understand its strengths and weaknesses so you can make an informed choice about your IT needs. If you have questions about cloud business solutions or other IT related issues please contact us, we are always ready to help you boost your business.
How Safe is Cloud Storage?
While still a relatively new innovation, and despite hackers attempts at scaring consumers, cloud storage is a safe way to store your data. We need to examine how secure the cloud is and what measures cloud storage providers use to protect your data.
Cloud Coverage
Cloud services are inherently invested in keeping your data safe, the success of their business depends on their reputation for secure data management. The main form of defence in any cloud storage system is encryption which utilises complicated algorithms to ensure the safety of your data. A second form of protection is offsite storage which prevents most employees from accessing the servers. These storage facilities use measures such as guards, round-the-clock monitoring, and fingerprint locks to secure their data.
Security Protocols
Let’s further examine the “why” portion to answering, “How safe is cloud storage?” because these are the causes behind making cloud storage so secure. Cloud service providers are more aware of threats to security than the typical consumer and provide higher security than that found on home computers, so what does that entail?
Built-in firewalls
These restrict the flow of information entering a network by stipulating what is allowed into it. Firewalls are built to keep suspicious traffic out which makes it difficult for viruses to get into your data.
Redundancy
This is exactly what it sounds like, your data is copied many times then stored on different servers and, ideally, servers that are in multiple locations. It is greatly beneficial when hardware fails or there is a software glitch, as in 2014 when Dropbox irretrievable lost customer files. Having a spare to rely on can help prevent disaster and keep your business operating smoothly.
Security Updates
Cloud storage companies regularly update their security to maximise the strength of the defensive measures. Personal users may often may a bit more relaxed in this regard but your cloud service provider will always remember to consistent improvements to their security measures.
Event Logging
Your networks form of keeping a diary, log records document network actions which can help analysts increase their understanding of threats. Studying the factors behind an attack increases your cloud storage provider’s ability to predict and stop security violations.
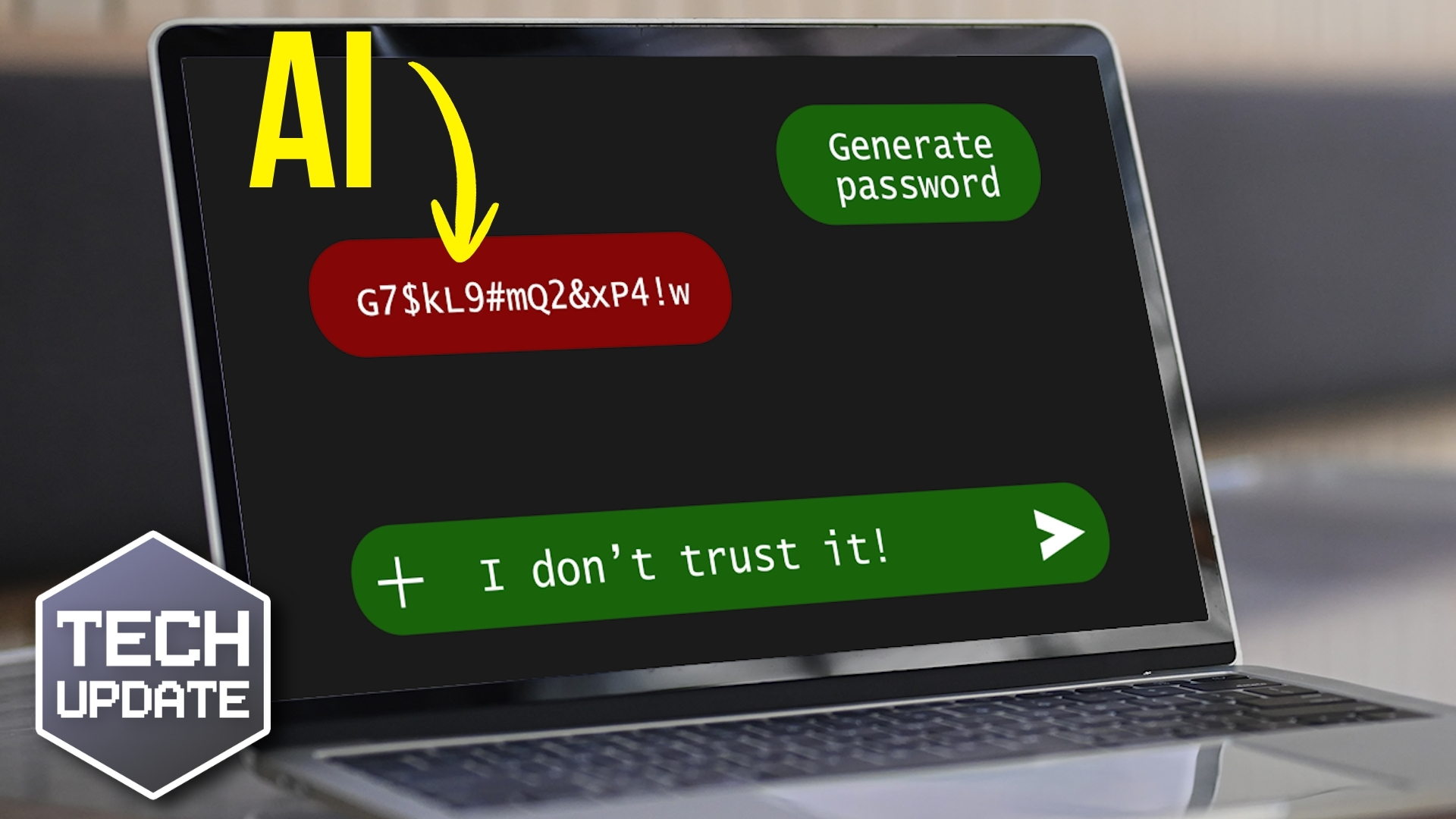
AI
Artificial intelligence is being used to look after your data and keep it safe through useful feedback. AI can be programmed to search and identify weaknesses in security measures which provides an opportunity for assessment and improvement.
Intrusion Detection
Identifying who is attempting to steal your data is an excellent countermeasure to intruders. The initial breach of a multi-layered defence system can give cloud storage providers time to diagnose who is committing the attack and prevent them from going further.
Invest in Deterrence
Understanding the strengths and weaknesses of your data security system before an attack happens is a sound step towards greater security. Ensure you are using the best and most secure cloud storage solutions available by requesting a FREE IT Health Check from Connected Platforms or learn more about the information technology in your business. We welcome calls on (07) 3062 6932 or contact us online for an obligation free consultation on ways to improve how you store your critical information.