Human error is estimated to be responsible for as many as 95% of data breaches. Users get fooled by clever phishing campaigns, use poor password security, email sensitive data without encryption, among other security mistakes.
While many small businesses understand the importance of network security and using tools like firewalls and next-gen antivirus to keep up with increasingly dangerous online attacks, they don’t always prioritise employee training.
Employees are the key target of most online attacks because a majority of them initiate via phishing email. Keeping your employees well-trained on how to tell a fake email from a real one can significantly boost your company’s security level and reduce risk.
Having a team that is well-trained in security awareness can reduce an organisation’s risk of a cyberattack by up to 70%.
What does good employee cybersecurity training look like? It doesn’t look like a one-hour session on security once per year. It involves multiple touchpoints and learning opportunities that keep data security top of mind.
Some of the ways to do this include:
- Weekly IT security tips sent in a company newsletter or other communication
- Short videos that focus on one key cybersecurity element
- Webinar sessions
- Tip sheets & posters
- Phishing simulations
- Incident response drills
One way that you can help employees sharpen their phishing detection skills is to use the SLAM method.
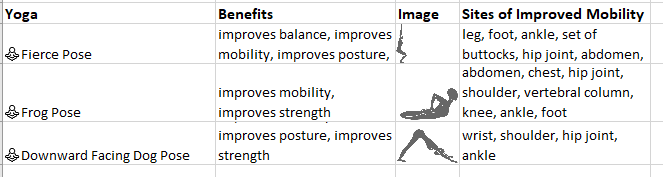
SLAM stands for four key areas of an email that a user should check for potential phishing:
- Sender
- Links
- Attachments
- Message
Teaching Employees the SLAM Method
SLAM provides an easy-to-remember acronym for the areas of a message that someone should check thoroughly before taking any action on the message.
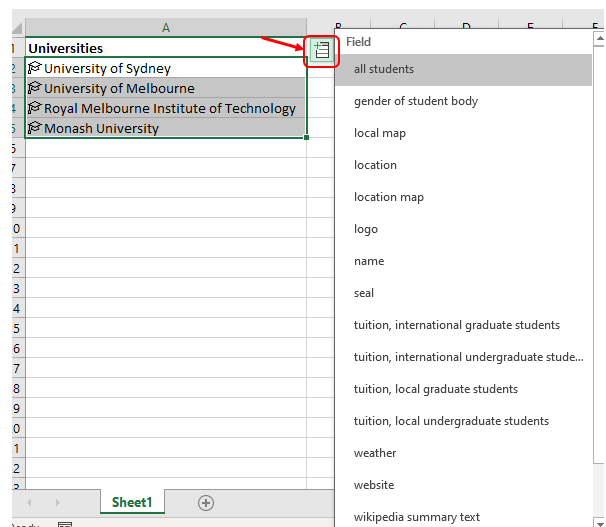
Sender
The name you see in the “From” line of an email isn’t necessarily the same person or entity that sent the message.
Email spoofing is used often and is when the scammer fakes an email address as the sender to trick the recipient into trusting the source of the email. There are typically two ways this is done:
- Use code to fake a real email address (it might even look like it’s coming from inside your company)
- Use a close fake address that appears to be real, but isn’t.
One example of using a close fake is this email that appears to be from the US-based bank, Bank of America. The email address used as the sender is “[email protected]”
A quick Google search on that email address quickly reveals this email to be a phishing scam.
You should carefully check out the sender of the email and don’t just trust the address you see.
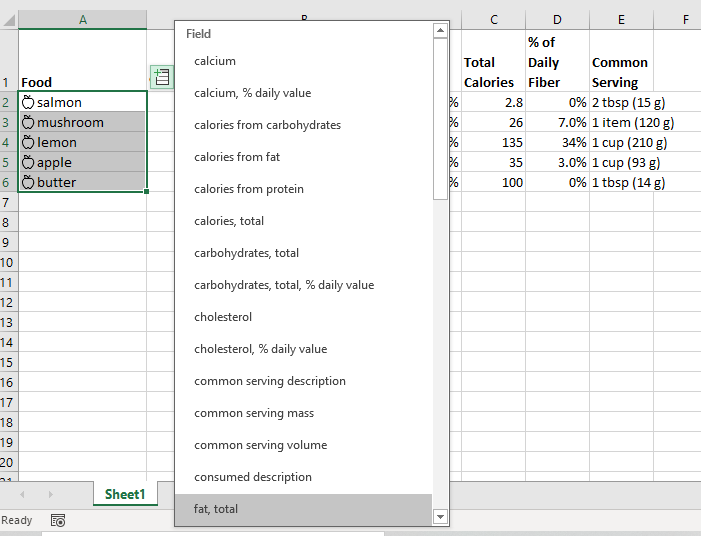
Links
Hyperlinks are now used in a majority of phishing emails. They can get by programs looking for dangerous file attachments and users tend to trust links more than attachments.
Links are just as dangerous as file attachments and can lead to fake login forms designed to steal login credentials. They can also direct the user to a site that will infect their device with malware as soon as the page loads.
Rules of thumb for dealing with links in emails are:
- Hover over all hyperlinks before clicking them
- When possible, go to a website directly, instead of through a hyperlink in an email
- Use a DNS filter that can block malicious websites if a user accidentally clicks a dangerous link
Attachments
Many employees know to be wary of strange file attachments, like a .exe or .tar file. However, they tend to trust file attachments like Word and PDF. But these innocent-looking file types can also be weaponised by phishing scammers.
Users should not open attachments if they do not know with 100% certainty that the sender is legitimate, and the file is safe. It’s important to have a program that scans all email attachments for viruses and other types of malware.
An additional security step is to disable the running of macros in Word and Excel documents, as these are used to distribute malware hidden in those file types.
Message
The body of the email message should also be checked thoroughly for any signs that an email may not be quite right. This includes looking for any typos or grammatical errors.
Additionally, look for any terms that aren’t commonly used in your country or that sound strange.
These small clues can be difficult to see if you “speed read” through the text of the email. Look carefully to identify any errors.
For example, in this email we posted above in the Links section, if you look carefully at the second sentence, you’ll see a mistake that is a phishing giveaway. The sentence says, “We confirmation that your item has shipped” instead of “We confirm that your item has shipped.”
Amazon would not make such a glaring grammar mistake.
Need Assistance Keeping Your Team Well-Trained in IT Security?
You don’t have to go it alone when it comes to security awareness training. Connected Platforms can help your Brisbane area business with an ongoing program that sharpens your team’s cybersecurity skills.
Contact us for a free consultation. Call (07) 3062 6932 or book a coffee meeting online.